French startup Bankin’ has introduced Bridge Pay this week, an API that lets you initiate payments using bank transfers from your app. Think about it as a sort of Stripe, but for bank transfers. The API currently covers 12 major French banks, which represent around 90% of retail bank accounts in France.
Bankin’ is both a B2B and B2C startup. It operates a popular consumer app that lets you aggregate all your bank accounts in a single app. The company has managed to attract 4 million customers with this app. Bankin’ also manages an API called Bridge. Developers can connect directly with bank accounts to fetch transactions and banking information.
With Bridge Pay, the company wants to go one step further and become a payment API as well. The company has been using Bridge Pay within Bankin’ already — customers can transfer money from one bank account to another in the Bankin’ app. Bankin’ users have transferred €1 billion so far.
Third-party companies will now be able to initiate bank transfers themselves. It could be useful for e-commerce companies that sell very expensive items for instance. For example, if you want to buy expensive airplane tickets or a Mac Pro on Apple’s website, you might reach your card transaction limit.
It also opens up a ton of possibilities when it comes to automating B2B transactions without having to interact with your bank account. For instance, payroll services could integrate directly with your company’s bank account to transfer money to your employees.
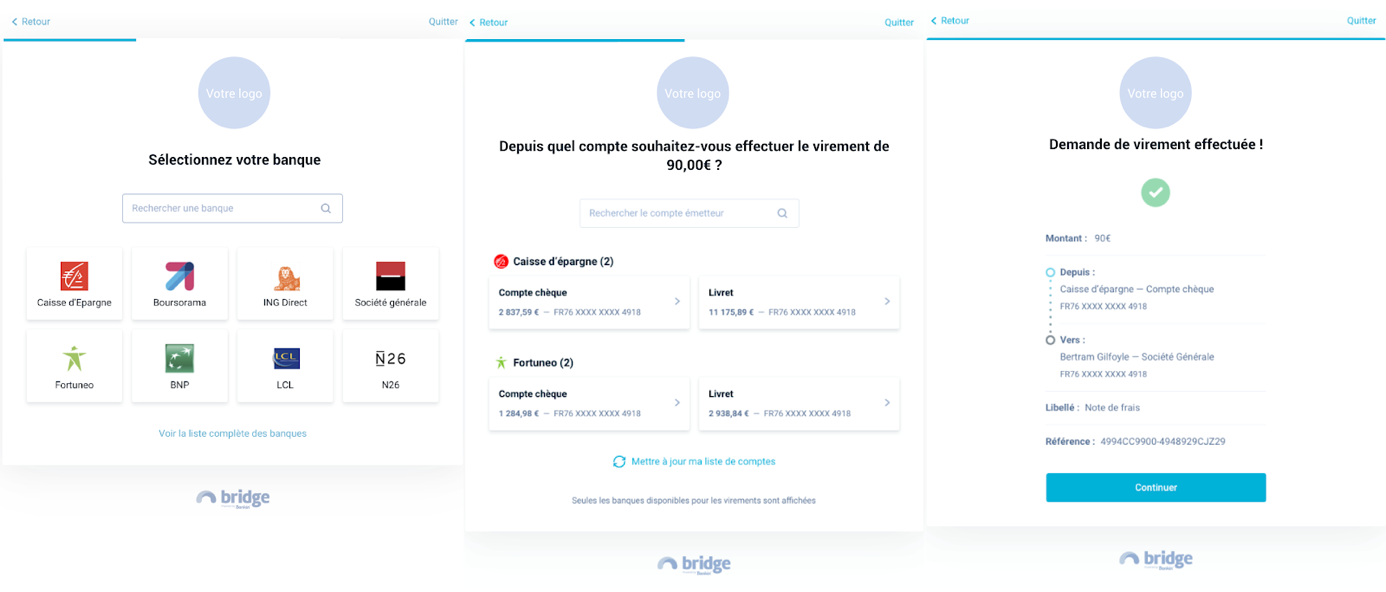
Bridge Pay can be integrated directly in your app or service. When you select payment via bank transfers, you get a list of banks, you then connect to your bank account, choose an account and initiate a payment. Chances are your bank is going to ask you for a confirmation via a text message or a push notification. The company can add more banks in the future without any change in the app.
from TechCrunch https://ift.tt/38Lx9av
Comments
Post a Comment