No, it’s not the kind of honeycomb you’re probably thinking of. We’re talking about the lightweight panels commonly used in aerospace applications. Apparently they’re rather prone to dents and other damage during handling, so Boeing teamed up with students from the California State University to come up with a way to automate the time-consuming repair process.
The resulting machine, which you can see in action after the break, is a phenomenal piece of engineering. But more than that, it’s an impressive use of off-the-shelf components. The only thing more fascinating than seeing this robotic machine perform its artful repairs is counting how many of its core components you’ve got laying around the shop.
 Built from aluminum extrusion, powered by an Arduino Due, and spinning a Dewalt cut-off tool that looks like it was just picked it up from Home Depot, you could easily source most of the hardware yourself. Assuming you needed to automatically repair aerospace-grade honeycomb panels, anyway.
Built from aluminum extrusion, powered by an Arduino Due, and spinning a Dewalt cut-off tool that looks like it was just picked it up from Home Depot, you could easily source most of the hardware yourself. Assuming you needed to automatically repair aerospace-grade honeycomb panels, anyway.
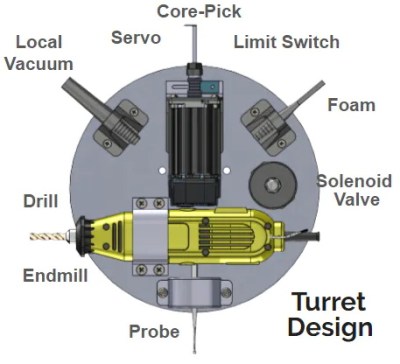
At the heart of this project is a rotating “turret” that holds all the tools required for the repair. After the turret is homed and the condition of all the cutting tools is verified, a hole is drilled into the top of the damaged cell. A small tool is then carefully angled into the hole (a little trick that is mechanical poetry in motion) to deburr the hole, and a vacuum is used to suck out any of the filings created by the previous operations. Finally a nozzle is moved into position and the void is filled with expanding foam.
Boeing says it takes up to four hours for a human to perform this same repair. Frankly, that seems a little crazy to us. But then again if we were the ones tasked with repairing a structural panel for a communications satellite or aircraft worth hundreds of millions of dollars, we’d probably take our time too. The video is obviously sped up so it’s hard to say exactly how long this automated process takes, but it doesn’t seem like it could be much more than a few minutes from start to finish.
from Hackaday https://ift.tt/3crwIEZ
Comments
Post a Comment