LIDAR has gained much popularity as a means for self-driving cars to survey the space around them. At their most basic, LIDAR is a surveying method that uses lasers to paints the space around the sensors and assembles the distances measured from reflected light into a digital three-dimensional representation. That’s something that has quite a number of other applications, from surveying ancient ruins and rainforests from a bird’s eye view to developing 3D models of indoor spaces.
 One fascinating use of LIDAR technology is to map out the routes inside caves, subterranean spaces that are seldom accessed by humans apart from those with specialized equipment and knowledge of how to safely traverse the underground terrain. [caver.adam] has been working on his Open LIDAR project for a few years using an SF30-B High Speed Rangefinder and laser device for a dual-system atop a gimbal with stepper motors for cave scanning.
One fascinating use of LIDAR technology is to map out the routes inside caves, subterranean spaces that are seldom accessed by humans apart from those with specialized equipment and knowledge of how to safely traverse the underground terrain. [caver.adam] has been working on his Open LIDAR project for a few years using an SF30-B High Speed Rangefinder and laser device for a dual-system atop a gimbal with stepper motors for cave scanning.
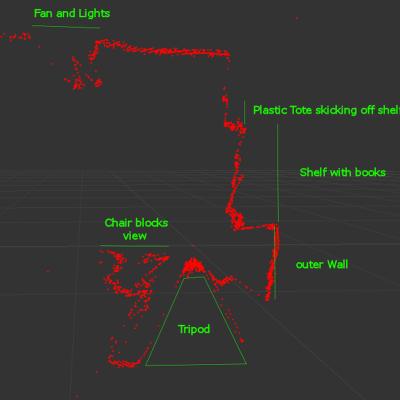
Originally an entry in the 2016 Hackaday Prize, [Adam] has continued to work on the project. The result shown in the video below is a cheaper 3D LIDAR setup that works by rotating the laser distance module on 2 axes with a sensor centered at the center of rotation. It works for volumetric calculations, detects change over time, and identifies various water patterns and rocks on a surface map. Compared to notebooks, tape measures, and compasses, it’s certainly a step up in cave surveying technology.
Check out some other past underground surveying projects, such as Iowa City’s beer caves scanning projects and National Geographic’s 2014 expedition of the Titan Chamber in southern Guizhou Province in China.
from Hackaday https://ift.tt/39p8aL9
Comments
Post a Comment