Inspired by the good old days when your computer would boot directly into BASIC, [Le Roux Bodenstein] has created a handheld device he calls “DumbDumb” that can drop you into a MicroPython environment at a moment’s notice. If that doesn’t interest you, think of it this way: it’s a (relatively) VT100 compatible serial terminal with a physical keyboard that can fit in your pocket.
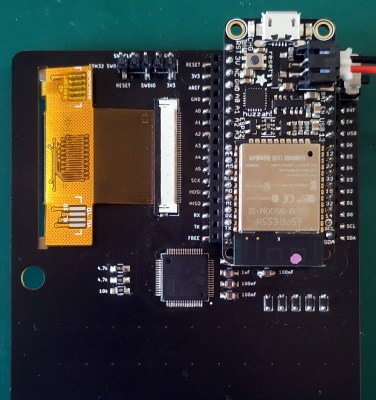 Being essentially just a dumb terminal (hence the name), there’s actually not a lot of hardware on the board. Beyond the 320×240 NewHaven 2.4 inch LCD, there’s just an STM32G071R8 microcontroller and a handful of passives. Plus the 57 tactile buttons that make up the keyboard, of course.
Being essentially just a dumb terminal (hence the name), there’s actually not a lot of hardware on the board. Beyond the 320×240 NewHaven 2.4 inch LCD, there’s just an STM32G071R8 microcontroller and a handful of passives. Plus the 57 tactile buttons that make up the keyboard, of course.
The MicroPython part comes in thanks to the spot on the back of the board that accepts an Adafruit Feather Wing. In this case, it’s the HUZZAH32 with an ESP32 on board, but it could work with other variants as well. With the wide array of Feather boards available, this terminal could actually be used for an array of applications.
So even if fiddling around with MicroPython isn’t your idea of a good time, there’s almost certainly some interesting software you could come up with for a tiny network-attached terminal like this. For example, it might be just what you need to start working on that LoRa pager system.
from Hackaday https://ift.tt/2SyN3QL
Comments
Post a Comment