Would you like to know the great thing about this community we have here? All the spitballing that goes on every day in the comments, the IO chat rooms, and in the discussion threads of thousands of projects. One of our favorite things about the Hackaday universe is that we help each other out, and because of that, our collective curiosity pushes so many designs forward.
 [Gurpreet] knows what we’re talking about. He’s back with version two of his self-playing kalimba, driven as strongly as ever by the dulcet tones of the Avatar theme. Now the robo-kalimba is rocking two full octaves, and thanks to your comments and suggestions, has relocated the servos where they can’t be picked up by the soundboard.
[Gurpreet] knows what we’re talking about. He’s back with version two of his self-playing kalimba, driven as strongly as ever by the dulcet tones of the Avatar theme. Now the robo-kalimba is rocking two full octaves, and thanks to your comments and suggestions, has relocated the servos where they can’t be picked up by the soundboard.
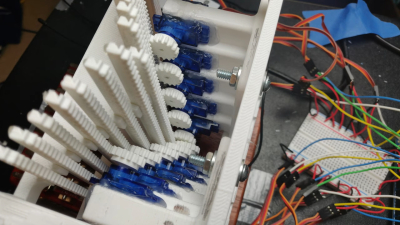
We gasped when we saw the new mechanism — a total of 15 rack and pinion linear actuators that make the kalimba look like a tiny mechanical pipe organ. Now the servos float, fixed into a three-part frame that straddles the sound box. [Gurpreet] melted servo horns to down to their hubs rather than trying to print something that fits the servos’ sockets.
Thumb your way past the break to check out the build video. [Gurpreet] doesn’t shy away from showing what went wrong and how he fixed it, or from sharing the 3D printering sanity checks along the way that kept him going.
Plucking kalimba tines is a difficult problem to solve because they’re stiff, but with timbre sensitive to many degrees of pressure. A slightly easier alternative? Make a toy player piano.
from Hackaday https://ift.tt/2HUiiPN
Comments
Post a Comment